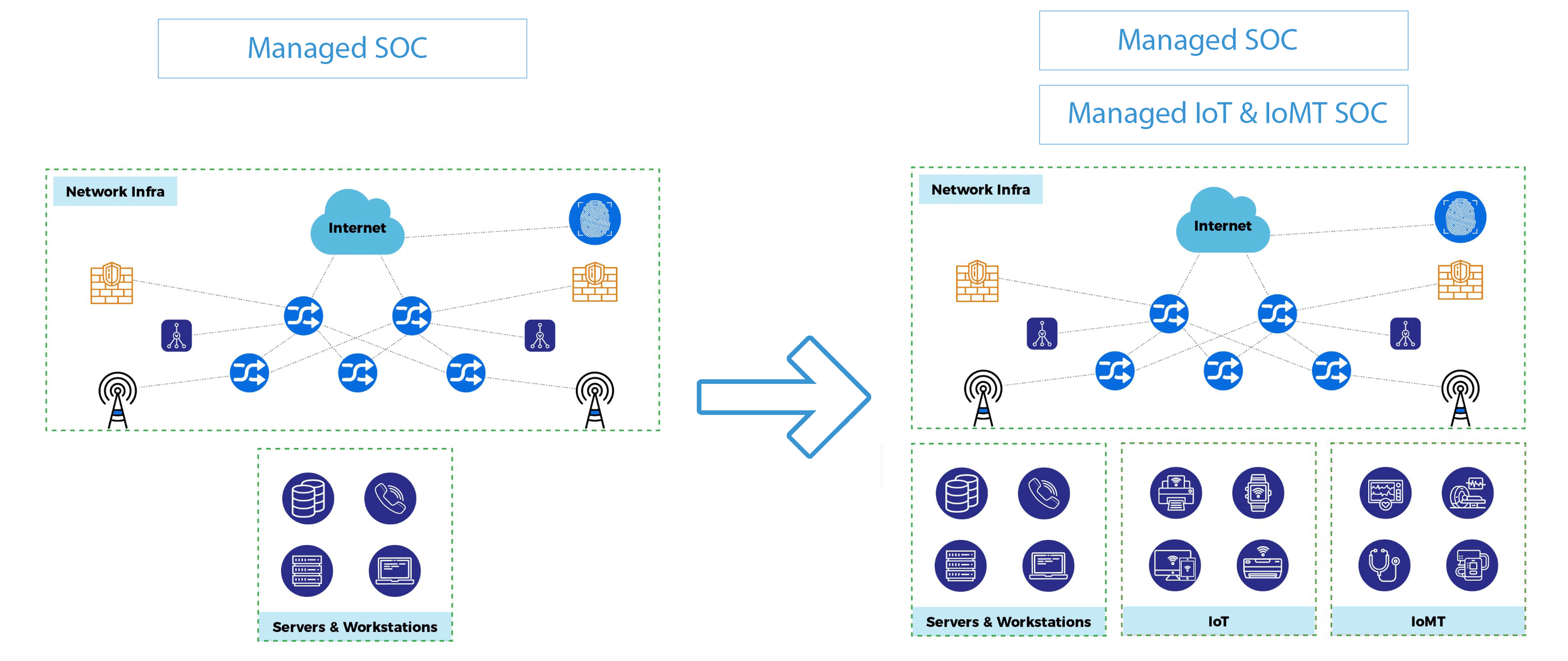
Our SOC experts detect, prevent, investigate, respond to, and analyze cyber threats with the latest technologies, as well as the best practices and procedures, to make sure that your hospital’s cybersecurity is up-to-date.
With a SOC, an organization can go into the depths of the network to discover all the significant weaknesses and build an active detection system thereon. This allows the security functions of your hospital devices to become more collaborative and faster.

Looking to secure all connected devices in your healthcare environment?
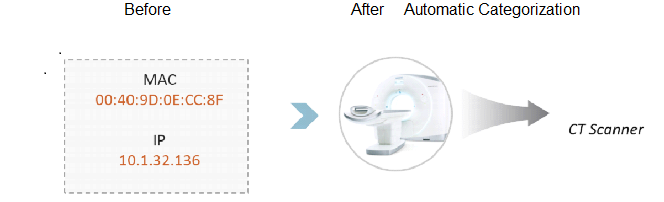
Every unmanaged, undetected, connected device including IOMT medical devices has exposure to various cybersecurity risks, PHI exposure risks, and Clinical risks.
Cybersecurity Risks
- Device Vulnerability.
- OS Identification.
- Endpoint Security State (MDS2).
- High-Risk Protocols.
- Communication Anomaly.
- External Communication.
PHI Exposure risk
- PHI presence.
- Manufacturer disclosure (MDS2).
- Behavior.
- Device Portability.
- Encryption at Rest/Transit.
Clinical Risks
- Physical Risk.
- Equipment Location.
- Mission Criticality (Availability).