Since 2010 software vulnerabilities have doubled every year, requiring organizations to constantly patch OS platforms and applications and audit security settings throughout their data network environment. To proactively address vulnerabilities before they are utilized for a cyberattack, organizations serious about the security of their environment perform vulnerability management to provide the highest levels of security posture possible.

The vulnerability management cycle
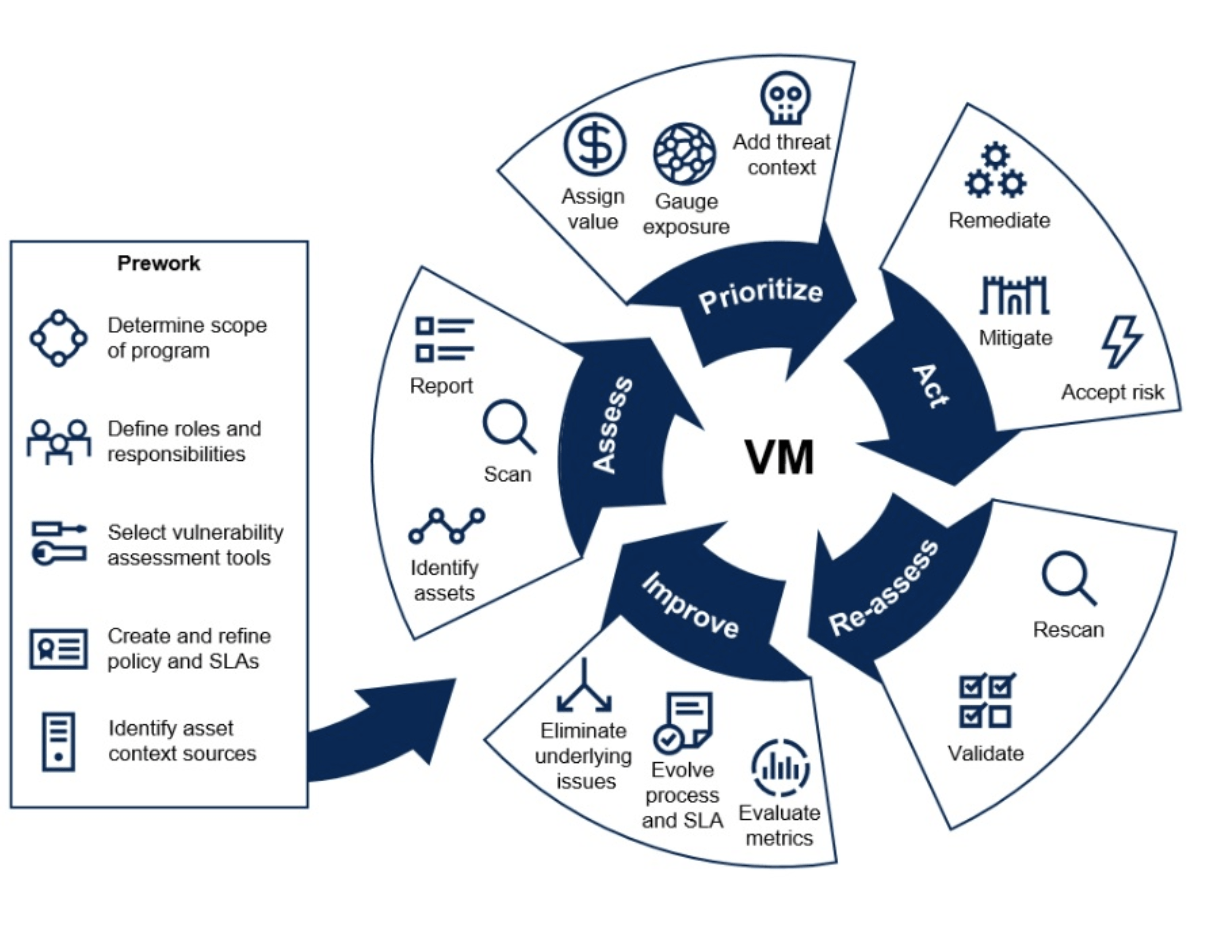
Source: Gartner




